What do racehorses and industrial machines have in common? Both reach peak performance once they have a tiny sensor attached.
For years now, manufacturers have been using small, internet-connected sensors to measure how machines are vibrating. They use that data to identify when performance is declining or the risk or breakdown is rising—and the sensors have been remarkably successful at helping manufacturers get more predictive, preventive, and proactive.
Of course, a running horse produces vibrations too. Sensors used to track vibrations for industrial applications can just as easily track them for equine applications. And once trainers have a reliable and accessible way to monitor every single stride of a horse’s performance, it will transform horse racing as we know it, and the equine industry more broadly.
In fact, it’s already happening.
Why Put Sensors on Horses?
Placed in the saddle cloth, these sensors weigh only a few ounces and track forces in four directions: up, down, forward, and back. Trainers can use that data to develop performance baselines for an animal, and then identify when performance deviates in any way.
That’s useful for two big reasons:
- Health and Wellness: Sensor data can help to flag health issues that might be invisible otherwise, and help to flag them early enough for trainers to intervene before injury occurs. The sensors take the guesswork out of vital health and safety decisions so that horses receive the best care possible.
- Training and Performance: Trainers know more about how horses develop when they can track how much and how quickly the sensor data changes. They can dynamically adjust training routines based on the data to help the animals achieve more than they could with past training methods informed more by observation than data.
These are just the two most obvious and exciting use cases, but many more will likely emerge as adoption increases—until one day when there’s a sensor in every saddle.
Getting Started with Sensors
Sensors are compact, inexpensive, and user-friendly. Plus, the sensors have been extensively studied in Australia, New York, and now by the Kentucky Horse Racing Commission, resulting in a rich pool of data to develop baselines and benchmarks to follow. This all makes it easy for trainers, racetracks, vets, and anyone else in the equine industry to adopt this game-changing technology.
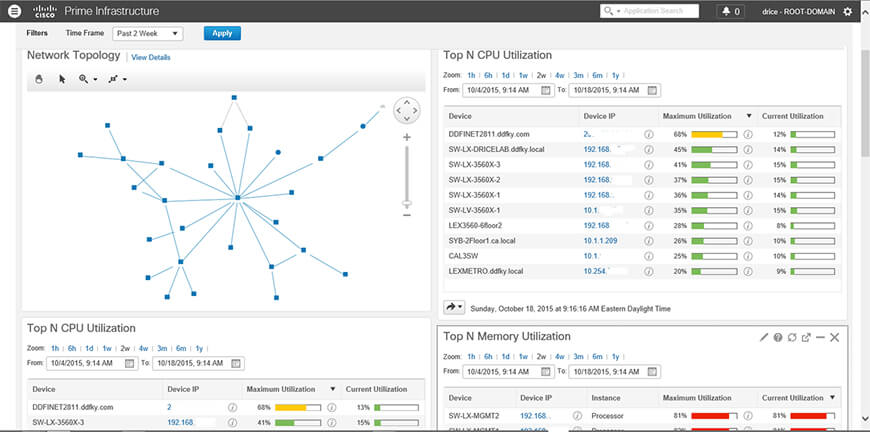
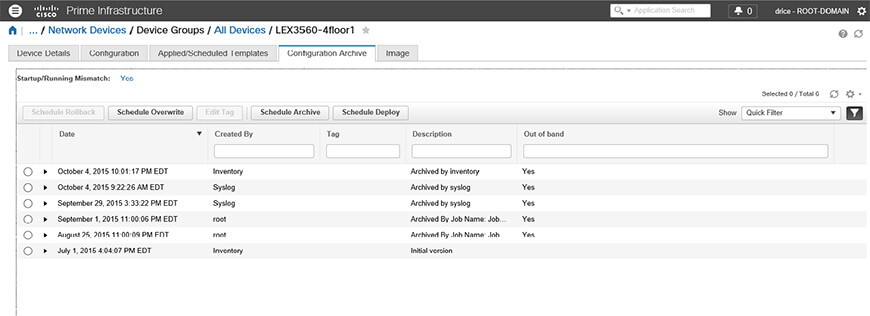
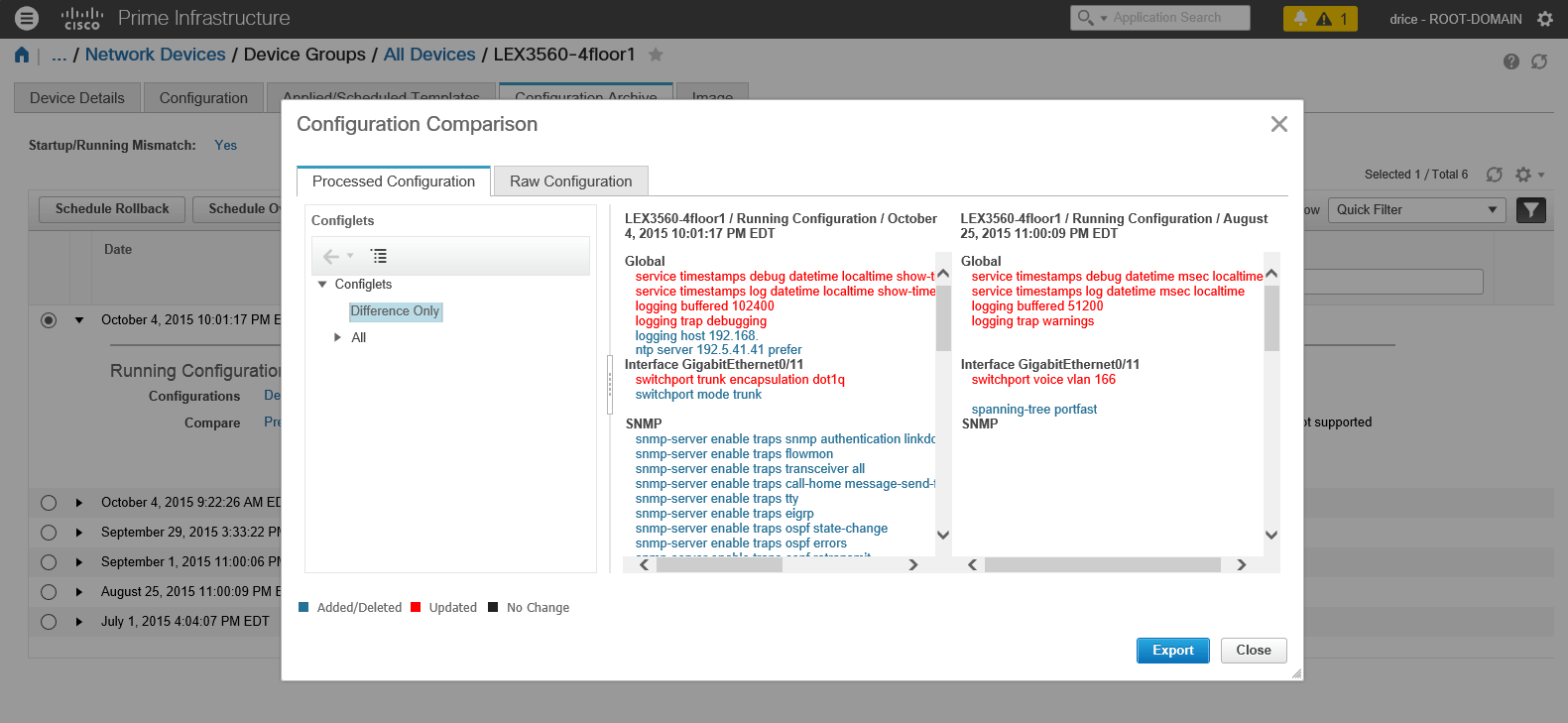
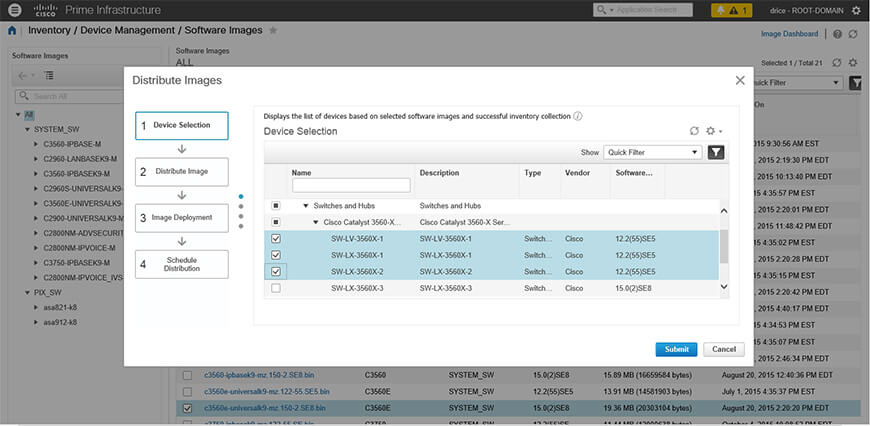
It takes more than just sensors, though. The space where the sensors will be used – racetrack, training facility, etc – needs a robust wireless network to transmit the data. It takes dedicated software to organize the raw data into a usable format and analyze results in real-time. With all these pieces in place, individual operators can begin using sensors—but the biggest beneficiary will be the equine industry as a whole as sensor data, continually collected from thousands of races around the world, connects us with horses like never before. With decades of experience in the equine industry, along with comprehensive technical expertise, Dean Dorton can help you integrate sensors into your operation. Contact us to learn more

 Contact Jason Miller (
Contact Jason Miller (